After you just cross the border of our country, the network provider sends you a lovely message, welcoming you back to your homeland. There is a pervasive sense that the location of every cell phone is constantly broadcast throughout the mobile network. You may be wondering, however, how this positioning really works. How do mobile carriers track the position of a cell phone?
Communication through a mobile phone would be impossible without the “base station,” also known as the transmission tower. A radio cell is a geographic area that a particular radio transmitter and receiver are capable of communicating. Mobile networks are comprised of a large number of these radio cells organized in the pattern of a honeycomb to provide comprehensive coverage.
The cell ID, or identification code, is a one-of-a-kind number that has been given to each of these individual cells. At the very least, the cell that the phone is now located in can be identified as long as it is powered on and registered with a cell tower.
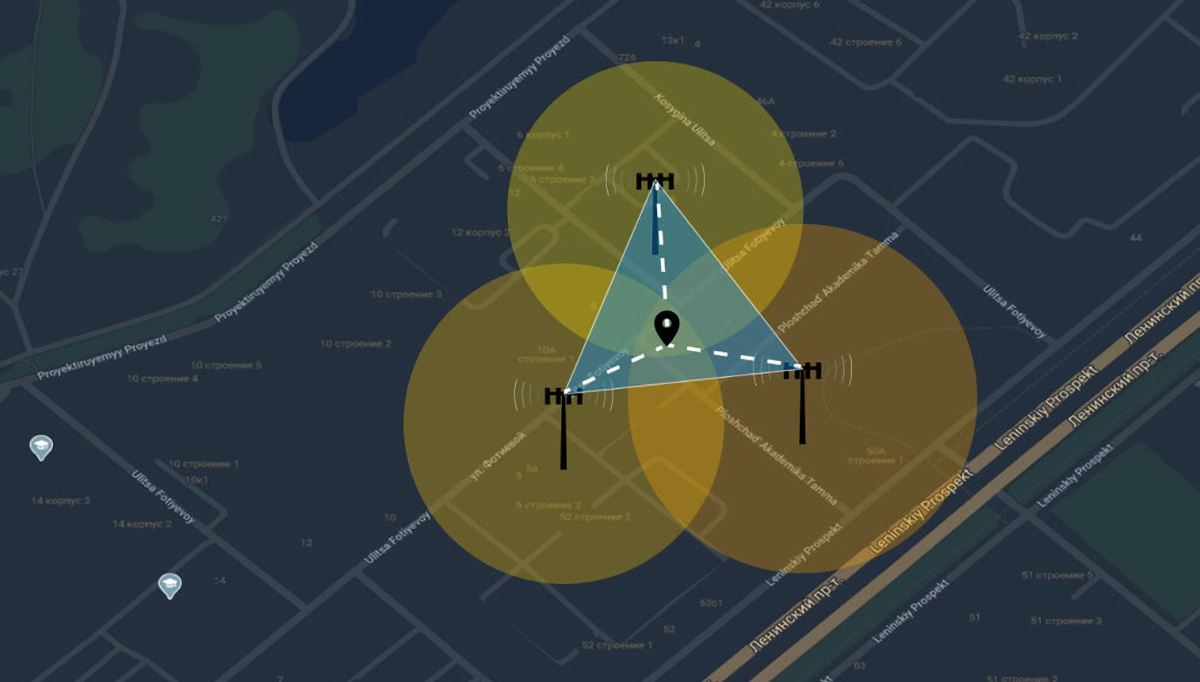
The time it takes for a cell phone signal to go in both directions can be used by service providers to estimate the phone’s approximate location. Cell tower triangulation is used by carriers to get a more precise reading; it does this by combining the locations of three cell towers. The primary goal of the development of this technology was to aid 911 dispatchers in locating callers.
Triangulation Enables Pinpoint Accuracy
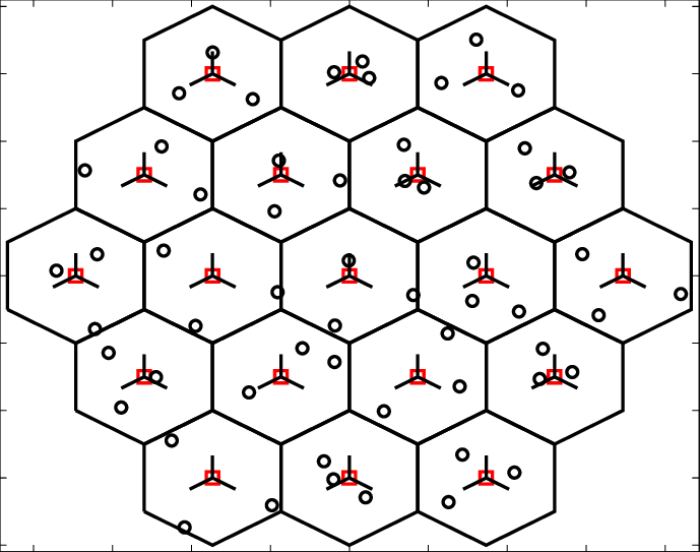
However, it is possible to determine this location with even greater precision. The cells that are next to one another overlap each other slightly, which creates a smooth transition from one cell to the next. The phone is connected to a number of different cells. In the case where the signal strength of the active cell starts to decrease, the phone will automatically move to the next cell which has a better signal.
Measuring the strength of the signal at each base station is one way to figure out how far apart the bases are. If at least three of these locations are used, it should be possible to estimate the position of the mobile phone within a few meters. This method of zeroing in on a location is referred to as triangulation.
This triangulation positioning is perfect for local promotions that can be accessed through mobile devices. The phone can then automatically display specific information about the location, for example the weather, the traffic situation or the schedule of the nearest movie theater.
With the triangulation method, it is also possible, but not guaranteed, to find devices that have been misplaced or stolen. Using an application that is made accessible by some service providers, it is possible to determine the location of a mobile phone while using another device, such as a computer at home.
Confidential Tracking
Turning on the mobile phone is sufficient for this, moreover, it doesn’t need to be in operational condition. The mobile service provider does not need anything else to obtain the connection data that is necessary for positioning. The method known as “silent SMS” is based on the same concept, and it is often used by law enforcement agencies during investigations.
When this occurs, the recipient’s phone won’t even ring, let alone display a notification that they have a message. The connection data is now created, and law enforcement can now obtain the phone’s location information from the service provider.
It is against the law in many countries to trace a phone without the authorization of the owner. It is impossible for suppliers of private surveillance services, even those with varying degrees of reliability, to disregard this fact.
However, if there is an urgent matter, or if a judge mandates the revelation of the position information, law enforcement officials may still get the location information they want. Concerns over this technique are often put forward by those who place a high value on protecting their personal information.